The internet is a vast realm, with many layers and hidden corners that often go unnoticed by the average user. Among these hidden areas lies the .onion link, a unique resource that opens up a different experience of the web. This article aims to demystify .onion links, how they work, and their purposes, all while empowering readers with essential knowledge that can enhance their online safety and privacy.
.onion Link
Spidering the Tor network provides a way to measure the breakdown of written languages on onion sites. Typosquatting is a tactic used by malicious actors on the surface web, and this has been taken to onion sites as well. While it was eventually recovered, the victimization and prolonged downtime is a typical example of the level of service found on onion sites. The data suggests that if you visit the Hidden Wiki onion page, you’d be about three clicks away from 82% of live onion sites. We also found that this tiny network of onion sites is tightly connected.
.onion links are associated with the Tor network, a special application designed to enhance privacy and anonymity online. When you visit a .onion site, your connection is routed through multiple servers, encrypting your data and making it difficult for anyone to trace your activity. This technology is especially significant for users in regions where internet access is restricted or surveilled.
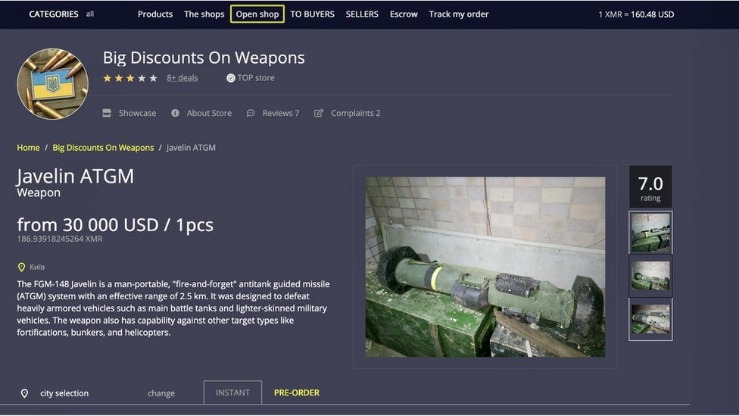
And if you think you’ve fallen victim to identity theft or fraud, be sure to report the internet scam just like you would any other crime. You can run a dark web scan to see if any of your data has leaked onto the black market. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material.
How .onion Links Work
- That means ZeroBin doesn’t know what you posted, because the encryption occurs on your computer before the data is sent to the server.
- An onion site uses the encrypted and anonymous Tor connection from your computer all the way to the websites you visit.
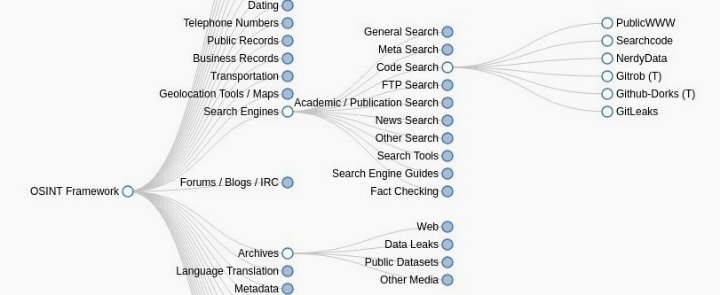
- Before using any dark web search engine, basic safety steps help reduce exposure to scams, malware, and identity risks.
- This just involves turning on your VPN before you open Tor and connect to dark web sites.
- The process costs a fee, but unlike other "tumbler" or "mixing" services, there is no risk that Wasabi or any of its users could scam you out of your coins.
The functionality of .onion links can be summarized in several key points:
- Anonymity: By using the Tor network, users can browse the web anonymously, which is a significant advantage for those wishing to protect their identity.
- Access to Restricted Content: .onion links provide access to websites that may be blocked or censored in certain locations.
- Enhanced Security: The multiple layers of encryption protect users from potential cyber threats and surveillance.
Types of .onion Sites
- This adds another, more reliable security layer to all of your online activity.
- These domains are not accessible through traditional browsers or outside the Tor network.
- An "alternative" search engine that's actually powered by Microsoft Bing.
- The Tor project still offers no official Tor apps for iPhone or iPad, but some third-party apps are available in Apple's App Store.
- We routinely include dark web reconnaissance in our assessments if there’s exposed data out there, we’ll find it and help you plug the leaks.
There are various categories of .onion sites available, each serving different purposes:
- Whistleblower Platforms: These sites facilitate anonymous reporting and sharing of sensitive information.
- Forums and Communities: Many forums discuss topics related to privacy, technology, and news while preserving users' anonymity.
- Information Resources: Certain .onion links host informational content regarding privacy rights and encryption methods.
Accessing .onion Links
To access .onion links, users must download and install the Tor browser, which is specifically designed for this purpose. Here’s how to get started:
- Download: Visit the official Tor Project website to download the Tor browser.
- Install: Follow the installation instructions applicable to your operating system.
- Browse: Once installed, open the Tor browser and enter any .onion link in the address bar.
Safety Tips for Browsing .onion Links
While browsing .onion links, it's crucial to maintain personal safety and security. Here are some guidelines:
- Use a VPN: While the Tor network offers anonymity, using a VPN can add an extra layer of security.
- Avoid Personal Information: Never share identifiable personal information on .onion sites.
- Use Secure Connections: Look for sites that provide HTTPS connections to ensure data integrity.
FAQs
What is a .onion link?
A .onion link is a web address that is part of the Tor network, aimed at providing anonymity and privacy for users.
Can anyone access .onion links?
Yes, anyone can access .onion links by using the Tor browser, which is specifically designed for this purpose.
Are .onion sites legal?
Many .onion sites operate legally, providing anonymity for various legitimate purposes; however, some may host illegal content. Users should exercise caution.
Understanding .onion links and the Tor network can significantly enhance one's online experience, opening new avenues for information and expression while maintaining anonymity. However, it demands a conscious approach to safety and security. Stay informed and browse responsibly!