The world of cybersecurity is ever-evolving, with new threats and vulnerabilities emerging daily. One of the terms that has gained attention in recent discussions is 0day onion. This article aims to provide a clear understanding of what a 0day onion is, its implications, and the necessary precautions one should consider to stay informed and safe in the digital realm.
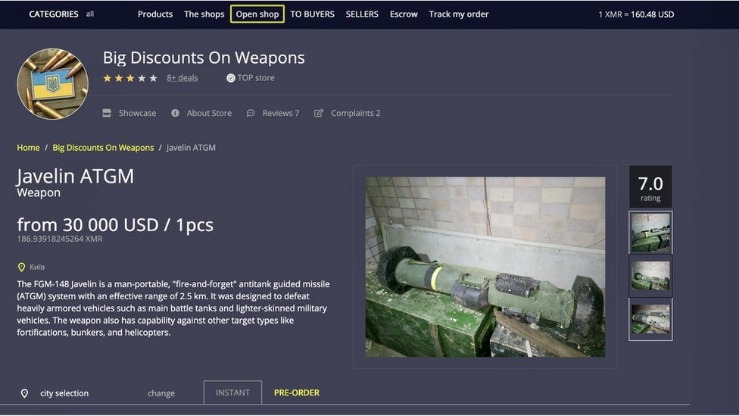
These are mostly application-specific vulnerabilities and bugs, but in many cases, can be easily exploited by attackers. The group’s operator, LockBitSupp, acknowledged the incident in a Tox conversation with Rey but insisted that no private keys or critical data were lost. Over the last month, a darknet marketplace calling itself TheRealDeal Market has emerged; it focuses on brokering hackers’ zero-day attack methods. Prosecution requires evidence gathering that conflicts with the fundamental right against self-incrimination and clashes with the privacy protections afforded to legitimate users of anonymizing networks.
The quintessential day-neutral onion, Candy is adaptable to nearly every climate and region. If we missed any noteworthy websites or databases you find vital to a penetration testers arsenal, be sure to leave a comment and share your picks. Its rules ban only child pornography and, strangely, services that offer “doxing,” the posting of specific users’ private information. A broad server network can be advantageous for accessing various regions, while fast and reliable connections are essential for safe streaming. Surfshark One — a cybersecurity bundle for all-over protection. Proton Pass is a cross-platform password manager that provides encrypted storage, password generation, and security monitoring features with integrated 2FA and dark web monitoring capabilities.
What is a 0day Vulnerability?
A 0day vulnerability refers to a security flaw in software that is unknown to the vendor and, consequently, has not been patched. The term “0day” indicates that the vulnerability has been exploited by hackers before the developer has had any time to address it:
- Onion.name is a dark web resource that helps make sense of the mess of letters and symbols that usually form the darknet sites.
- In 2024, Operation Cronos, a global law enforcement initiative, successfully took down 34 of LockBit’s servers and seized decryption keys, stolen data, and cryptocurrency wallets.
- The discovery of a new 0day flaw can be a seismic event, and the community on a trusted secure marketplace is typically among the first to know, analyzing its potential impact and value away from the scrutiny of the public internet.
- The exploit is deployed silently, ideally without triggering any alarms, to establish a persistent presence on the target systems.
- Unpatched vulnerabilities can be used to execute arbitrary code.
- They often lead to unauthorized access or data breaches.
- Cybercriminals can sell these vulnerabilities on the dark web.
The Concept of Onion Routing
Onion routing is a method of anonymous communication over a computer network. It encrypts data in layers (like an onion), allowing for a secure and private exchange of information. When combined with 0day vulnerabilities, it presents a unique situation:
- Hackers may exploit 0day onion to conceal their activities.
- Onion routers can mask the source of attacks, making detection difficult.
- Users utilizing onion routing need to be cautious of potential vulnerabilities.
Implications of 0day Onion Vulnerabilities
The implications of 0day onion vulnerabilities can be severe. As these vulnerabilities get exploited:

- Organizations might face significant financial losses.
- Data breaches can lead to the exposure of sensitive information.
- Reputation damage can ensue if users feel their data is not secure.
Staying Safe: Best Practices
To protect yourself against 0day onion vulnerabilities, consider adopting the following best practices:
- Regularly update software and applications to minimize vulnerabilities.
- Utilize comprehensive cybersecurity solutions that can detect unusual activities.
- Educate yourself and others about the latest cybersecurity threats.
- Implement strong passwords and two-factor authentication to add an extra layer of security.
FAQs about 0day Onion

What is the difference between 0day and zero-day?
There is no difference; both terms refer to the same concept: vulnerabilities that have not yet been discovered by the software vendor.
- We then stored all the contents of each "category" (e.g. dos-poc) in corresponding directories.
- In conclusion, understanding the concept of 0day onion is essential for anyone interested in cybersecurity and the underground digital landscape.
- Get a live demo of our security operations platform, GreyMatter, and learn how you can improve visibility, reduce complexity, and manage risk in your organization.
- As the black market continues to thrive, especially among those who seek to exploit these vulnerabilities, the pressing need for a robust ethical framework becomes increasingly apparent.
- The distribution chain is intentionally opaque, designed to protect the identity of all parties and to maintain the exclusivity and value of the exploit for as long as possible before its eventual discovery and patching by software vendors.
Can 0day vulnerabilities be reported anonymously?
Yes, individuals can report vulnerabilities anonymously to encourage responsible disclosure practices.
How can I find out about new 0day vulnerabilities?
Keeping up with reputable cybersecurity blogs and forums can provide insights into newly discovered vulnerabilities.
Are 0day attacks illegal?
Yes, exploiting 0day vulnerabilities for malicious purposes is illegal and can result in severe legal consequences.
Understanding 0day onion vulnerabilities is essential for anyone engaged in the digital world today. By staying informed and adopting proactive security measures, individuals and organizations can protect themselves from becoming victims of cyber threats.