As technology continues to evolve, so does the landscape of online marketplaces, including those operating on the darknet. By 2026, the dynamics of these markets have changed significantly, influenced by advancements in cybersecurity, law enforcement techniques, and user preferences. Understanding how these platforms function can empower individuals to navigate the internet more safely and securely.
2026 Working Darknet Market
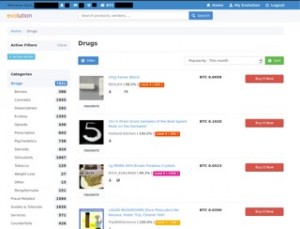
The darknet market is a part of the internet that requires specific software, configurations, or authorization to access. Here, users can buy and sell a wide variety of goods and services, though many transactions involve illegal items. To better understand the characteristics and operations of the 2026 working darknet market, we can explore several key aspects.
- On July 31, the Italian police in conjunction with Europol shut down the Italian language Babylon darknet market seizing 11,254 Bitcoin wallet addresses and 1 million euros.
- Just Onion is a curated directory of .onion sites organized by category.
- Fraud shops are services found mainly on the dark web that sell stolen data and personally identifiable information (PII), which cybercriminals use for scams, identity theft, and ransomware attacks.
- Professional dark web monitoring platforms solve the limitations of manual search.
- This aligns with broader law enforcement efforts to dismantle crypto-enabled criminal networks, as seen in recent global operations targeting malware-as-a-service and infostealer platforms.
Features of Darknet Markets
Maintain market integrity with proactive regulatory monitoring tools Mission-critical tools and datasets to thwart complex crypto-enabled crime According to the initial SDNY criminal complaint, investigators were able to trace the domain for the marketplace to Lin as he used his real name along with a phone number and address in the registration process. Prosecutors said the platform processed more than $105 million in illegal drug sales between October 2020 and March 2024, facilitating more than 640,000 transactions and serving hundreds of thousands of buyers worldwide Attorney’s Office for the Southern District of New York, bringing to a close one of the largest online drug market prosecutions since Silk Road.
Without continuous monitoring, security teams are always reacting to breaches that threat actors discovered first. Stolen credentials can appear on automated marketplaces within hours of initial compromise. Transactions are conducted in cryptocurrency, typically Bitcoin or Monero, with funds held in escrow by the marketplace until the buyer confirms receipt.
Some contain harmful or illegal content, and others may lack encryption or expose users to tracking risks. Security professionals use these tools to track cybercriminal activity, uncover leaked credentials, and identify potential threats before they escalate. We automate contextualization to reduce false positives while accelerating threat detection, enabling your security teams to take proactive defensive actions before threats materialize into costly incidents. We at KELA help you move beyond basic dark web monitoring by providing real-time, contextualized intelligence from the cybercrime underground that focuses specifically on threats targeting your organization. Fresh Onions constantly crawls the dark web to discover and map new onion services as they appear.
- Anonymity: Users typically rely on cryptocurrencies like Bitcoin to keep their transactions private and semi-anonymous.
- Platforms: Various platforms have emerged, each with a unique interface and specific offerings, leading to a segmented marketplace.
- Censorship Resistance: Many darknet markets have developed robust systems to avoid shutdowns by government agencies.
- Escrow Services: To ensure fair transactions, most marketplaces provide escrow services that hold funds until both parties confirm satisfactory completion of the deal.
How to Access the 2026 Darknet Market
- This incident proved that data breaches are possible not only with legitimate businesses but also cybercriminal resources generating damage and operating on the Dark Web — which can have a much greater positive impact.
- Our platform sifts through vast amounts of underground data, providing complete context and visibility into security risks threatening your organization.
- These include the notoriously unreliable gun stores,citation needed or even fake assassination websites.
- Third, the marketplace model creates inherent tensions between escrow security, exit scam risk, and law enforcement vulnerability.
- The Tor Project has endorsed it since 2014, which gives it credibility other search engines lack.
- Download a Secure Browser: The Tor browser remains the most common method for accessing darknet sites securely.
- Use a VPN: While using Tor, a VPN can provide additional layers of security and anonymity.
- Navigate Safely: Know the common URLs for legitimate marketplaces to avoid scams and phishing sites.
Common Trends in 2026

As of 2026, several trends have emerged that shape the darknet market's operations:
- Increased Regulation: Governments are tightening laws and regulations, leading to market adaptation strategies.
- Shift to Privacy Coins: Users are increasingly opting for privacy-focused cryptocurrencies like Monero, which offer enhanced anonymity compared to Bitcoin.
- Focus on User Safety: Reputable markets implement stringent seller vetting processes to enhance user experiences and reduce scams.

Safety Precautions
While exploring or researching the darknet, it is crucial to prioritize safety. Here are some recommendations:
- Be Informed: Understand the risks involved and stay updated on cybersecurity best practices.
- Avoid Illegal Activities: Engaging in illicit transactions can result in severe legal consequences.
- Use Unique IDs: Create separate digital identities to minimize the risk of doxxing.
FAQs
Q1: Is the darknet always illegal?
A1: Not all activities on the darknet are illegal; there are legitimate uses such as privacy-focused communication.
Q2: Can law enforcement track darknet activities?
A2: Yes, while user anonymity is enhanced, authorities utilize advanced technology for tracking illicit activities.
Q3: How can I protect myself while browsing?
A3: Use a secure connection, consider a VPN, and remain cautious about sharing personal information.
The continuing evolution of the 2026 working darknet market illustrates the importance of remaining informed, aware, and responsible while navigating this part of the internet. By understanding how these markets operate, users can make informed decisions that prioritize their safety and security.